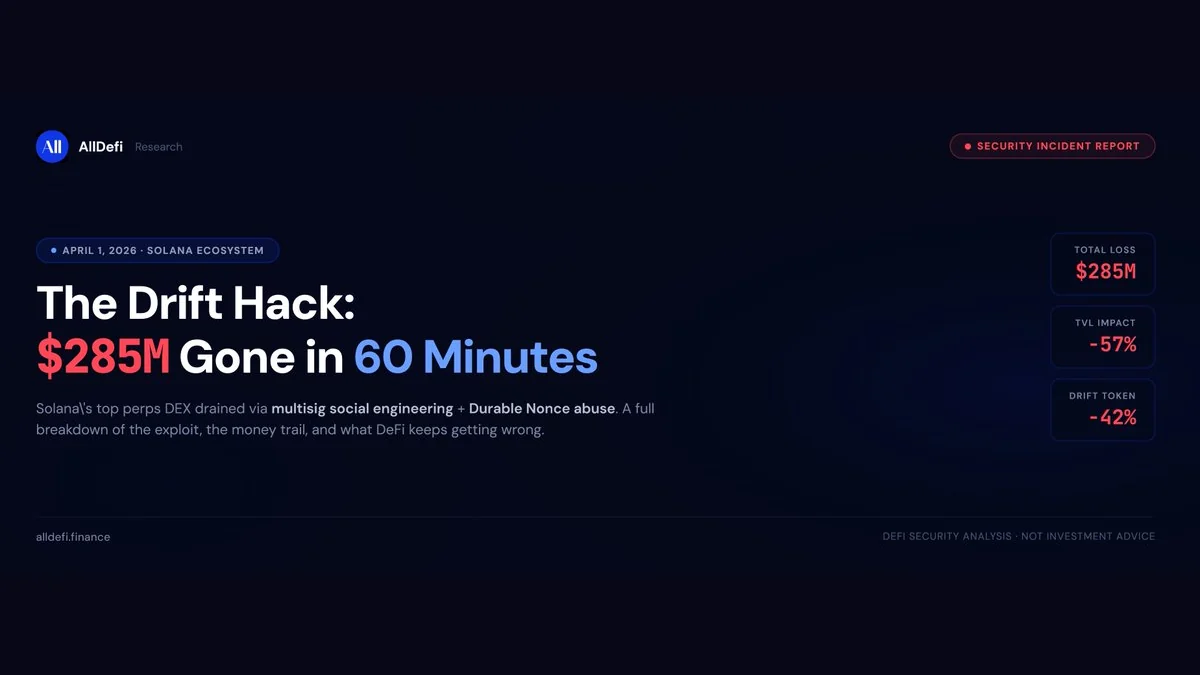
April 1, 2026. Solana's top perps DEX just got drained. This is how it happened, and what it tells us about a problem crypto still hasn't solved.
On the afternoon of April 1st, blockchain sleuths started pinging each other.
Money was leaving Drift Protocol — fast. Not thousands. Not millions. Hundreds of millions, pouring out of the protocol's main vault into a single unlabeled wallet starting with "HkGz4K."
Helius CEO Mert Mumtaz posted on X: "not 100% fully certain yet, but it seems drift might be getting exploited. monitor your positions."
The crypto community's first reaction? Must be an April Fools joke.
It wasn't.
Within 12 minutes, Drift's vault went from $309 million to under $41 million. By the time the dust settled, roughly $285 million in assets — USDC, JLP tokens, wrapped BTC, SOL, even Fartcoin — had been siphoned into the attacker's wallet and were already being swapped, bridged, and scattered across chains.
Drift confirmed the attack, suspended deposits and withdrawals, and posted what might be the most surreal disclaimer in DeFi history:
"This is not an April Fools joke."
What Actually Happened
Here's what makes this hack different from your typical smart contract exploit: Drift's code wasn't broken. Its access control was.
The attacker didn't find a bug in the protocol's Rust contracts. They didn't use a flash loan. They didn't manipulate an oracle in the traditional sense.
Instead, they went after the people who held the keys.
The Kill Chain
Step 1: Social engineering the multisig.
Drift's admin functions were protected by a 5-of-N multisig — the Drift Security Council. The attacker managed to obtain approval from 2 of the 5 signers. How? The leading theory is social engineering — tricking team members into signing what appeared to be legitimate transactions.
Two signatures. That's all it took to start the cascade.
Step 2: Weaponizing Solana's Durable Nonce.
This is where it gets technically interesting.
Normal Solana transactions expire in 60–90 seconds. But Solana has a feature called Durable Nonce — originally designed for offline signing and scheduled transactions — that lets you pre-sign a transaction and submit it whenever you want, days or even weeks later.
The attacker created nonce accounts weeks before the attack (around March 23–30), pre-signed the malicious transactions with the stolen multisig approvals, and waited. On April 1st, they submitted everything at once.
A time bomb, built on-chain, detonated on schedule.
Step 3: Amplifying the damage.
With admin control secured, the attacker didn't just transfer funds directly. According to recent analysis, they created a new spot market using a fabricated low-liquidity token (possibly the "CVT" token flagged in earlier reports), manipulated its oracle pricing, and used it as collateral to jack up internal withdrawal limits to absurd levels — reportedly 500 trillion USDC.
The safeguards designed to prevent large unauthorized withdrawals? Bypassed from the inside.
Step 4: Drain and run.
Eleven transactions. $155M in JLP tokens first. Then $51M in USDC, $10M in WSOL, $11M in cbBTC, plus a grab bag of other tokens. The vault was effectively emptied.
Step 5: Cross-chain laundering.
The attacker immediately began converting stolen assets to USDC, bridging to Ethereum via Circle's CCTP, and buying ETH — approximately 129,000 ETH (~$278M) as of the latest tracking. The funds are still being dispersed. The wallet remains active.
The Fallout
The market reacted exactly how you'd expect:
DRIFT token cratered from ~$0.072 to a low of $0.040 — a 40%+ drop. It's since crawled back to around $0.05, but confidence is shattered.
SOL briefly dipped to $83.82 but largely held up, suggesting the market views this as a Drift-specific failure rather than a Solana systemic risk.
Circle got dragged. ZachXBT publicly criticized Circle for not freezing the stolen USDC fast enough. When hundreds of millions are moving through your stablecoin infrastructure, response time matters — and Circle's wasn't good enough.
Collateral damage is spreading. Over 20 protocols with exposure to Drift — PiggyBank, Perena, Vectis, and others — have reported additional losses exceeding $10M combined.
The attribution question. Elliptic and other blockchain forensics firms have noted that the on-chain behavior patterns are highly consistent with previous DPRK / Lazarus Group operations. Official attribution is pending, but the playbook looks familiar.
The Bigger Picture: DeFi Keeps Breaking at the Same Spot
Here's the uncomfortable truth: we've seen this movie before.
Put Drift on a timeline with the biggest DeFi hacks of the past four years, and a pattern screams at you:
Ronin Bridge, March 2022 — $625M. Attackers compromised 5 of 9 validator keys through social engineering. The breach went undetected for six days. Attributed to Lazarus Group.
Wormhole Bridge, February 2022 — $325M. A signature verification flaw in the cross-chain bridge's smart contract. Pure code bug. Jump Crypto backstopped the full loss.
Euler Finance, March 2023 — $197M. Classic flash loan attack exploiting a logic flaw. The hacker actually returned most of the funds.
Bybit, February 2025 — $1.46B. Lazarus Group injected malicious JavaScript into Safe{Wallet}'s frontend. Signers thought they were approving routine transactions. They were handing over cold wallet control. The largest crypto theft in history.
Drift, April 2026 — $285M. Social engineering + Durable Nonce abuse + multisig compromise + oracle manipulation. No contract bug. All process failure.
See the pattern?
Three of the five biggest DeFi exploits in history — Ronin, Bybit, and now Drift — had nothing to do with smart contract vulnerabilities. The code was fine. The problem was who held the keys and how they were tricked into misusing them.
Multisig is supposed to be the answer to single-point-of-failure risk. But when signers can be socially engineered, when frontends can be hijacked, when pre-signed transactions can sit dormant for weeks waiting to detonate — multisig becomes a false sense of security.
What's New About Drift
While the root cause (key compromise) is depressingly familiar, Drift introduced a genuinely novel attack vector: the weaponization of Durable Nonce.
This is the first major exploit to use Solana's offline signing feature as a "time weapon" — pre-building the entire attack weeks in advance and executing it in a single coordinated burst. The attacker's wallet was created 8 days before the hack, with small test transactions on OKX and Jupiter. This wasn't an improvised smash-and-grab. It was a planned operation with rehearsals.
For the Solana ecosystem specifically, this is a wake-up call. Durable Nonce is a legitimate, useful feature. But any protocol using multisig governance on Solana now needs to account for the possibility that signed transactions can be stored and deployed later — potentially long after the signer has forgotten what they approved.
So What Needs to Change?
Every major hack generates the same cycle: shock, post-mortems, promises, then gradual complacency until the next one. But if the Drift hack has a single lesson worth internalizing, it's this:
"We have multisig" is not a security strategy.
Here's what a real security strategy looks like:
Timelocks on everything sensitive. If an admin action can drain the protocol, it should have a mandatory delay — 24 hours, 48 hours, whatever gives monitoring systems time to catch it. Pre-signed Durable Nonce transactions should trigger additional verification when submitted.
Transaction simulation before signing. Every multisig signer should see a human-readable simulation of what their signature will actually do. "You are approving a transfer of $155M in JLP tokens to wallet HkGz4K" is very different from a raw hex payload.
Signer security as a first-class concern. Hardware wallets. Air-gapped signing. Anti-phishing training. Regular rotation. If your signers are the last line of defense — and they are — treat them like it.
Stablecoin issuers need faster kill switches. Circle, Tether, and others sit at critical chokepoints. When $50M+ in stolen USDC is being bridged through your infrastructure, minutes matter. The current response time is not good enough.
Users need to diversify protocol exposure. "Don't put all your eggs in one basket" isn't profound advice, but half of Drift's TVL vanishing in an hour is a brutal reminder of why it matters.
Where Things Stand Now
As of April 3, 2026:
The attacker's wallets remain active. Funds are still being converted and dispersed. Drift's TVL has stabilized around $230M (down from $550M). Deposits and withdrawals remain suspended. No recovery plan has been announced.
The investigation continues. If the DPRK attribution is confirmed, recovery prospects are grim — Lazarus Group has historically been extremely effective at laundering stolen crypto through mixers, DEXs, and complicit exchanges.
For Drift's users, the waiting game continues. For the broader DeFi ecosystem, the question isn't whether another major exploit will happen — it's whether the industry will finally address the key management problem before it does.
From Ronin to Bybit to Drift, the story keeps repeating: the code holds, but the humans don't. Four years, three mega-hacks, one recurring failure mode. At some point, "human error" stops being an excuse and starts being a design flaw.
Sources: Drift Protocol official statements; PeckShield, Lookonchain, Elliptic on-chain reports; Bloomberg; CoinDesk; DeFiLlama; ZachXBT; Solana developer documentation on Durable Nonces.